
3CX Desktop App users compromised in a supply chain attack
3CX Desktop App users compromised in a supply chain attack After several cybersecurity companies raised the alarm about what appears to be an ongoing supply

3CX Desktop App users compromised in a supply chain attack After several cybersecurity companies raised the alarm about what appears to be an ongoing supply

The Tor browser installation contains malware that steals cryptocurrency Russian and Eastern European users have been the target of clipper malware since September 2022, which

Pakistan linked cyberattacks and the SideCopy Connection Cyberattacks have become increasingly common in recent years and they can have a devastating impact on individuals, organizations,

India blocks 500 apps over spoofing concerns On the recommendation of the Indian Cyber Crime Coordination Centre (I4C), Union Home Minister Amit Shah stated on
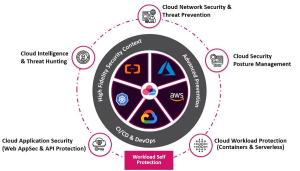
Cloud Computing: Risks, Challenges and Solution Cloud computing has many benefits, but it also poses significant risks and challenges for cybersecurity. Some of the risks

Phases of Incident Response and Planning Incident response planning is a critical component of cybersecurity. Developing an incident response plan involves creating a documented, organized

U.K. Crime Agency creates fake DDoS-for-hire to trap hackers The National Crime Agency (NCA) of the United Kingdom recently revealed that it has created a

Apple releases security update for Older iOS and iPadOS Models An actively exploited security hole was fixed by Apple on Monday and backported to previous

Twitter source code leaked online on Github Twitter has been in the news since the time it was bought by billionaire Elon Musk. With an increased

Microsoft fixes vulnerability in the Windows Snipping tool Microsoft provided an urgent security upgrade for the Windows 10 and Windows 11 Snipping tools to address
© 2024 -Latest Hacking Updates | Site Designed and Developed by – Traffic Tail

Subscribe to our weekly newsletter below and never miss the latest News.