Distributed Denial of Service (DDoS )attack type and mitigation
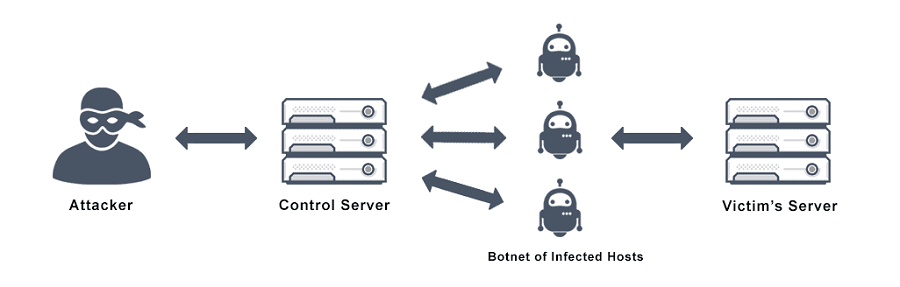
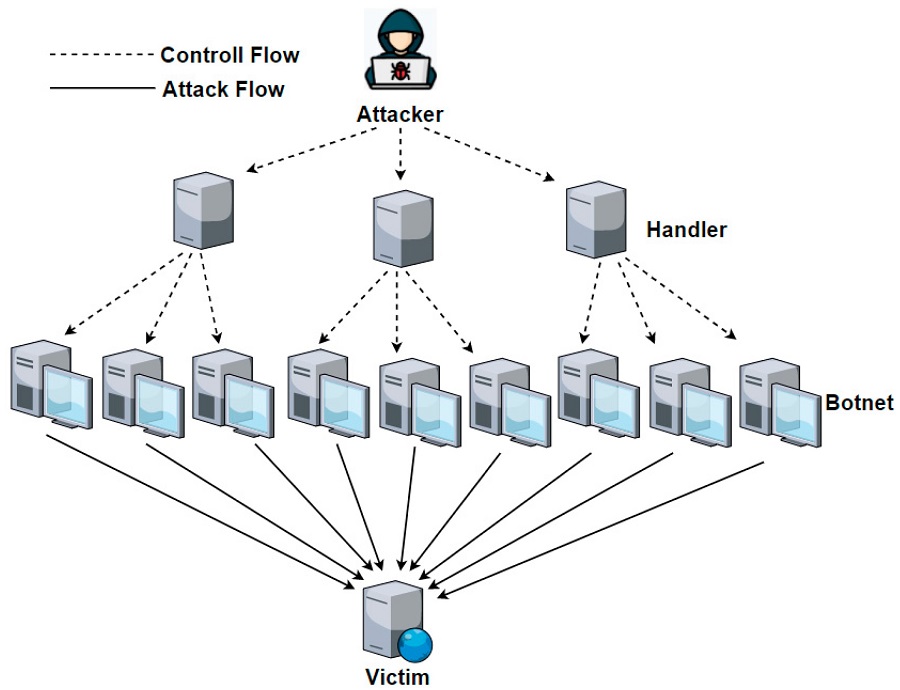
DDoS, or Distributed Denial of Service, is a type of cyberattack in which an attacker floods a target system with traffic to overwhelm it and cause it to become unavailable to legitimate users. DDoS attacks are often carried out using networks of infected computers, known as botnets, which are controlled by the attacker.
There are several types of DDoS attacks, including:
Volume-based attacks:
These attacks focus on overwhelming the target system with a large volume of traffic, such as UDP floods, ICMP floods, and amplification attacks.
Protocol-based attacks:
These attacks target the vulnerabilities in the communication protocols used by the target system, such as SYN floods and HTTP floods.
Application layer attacks:
These attacks target the application layer of the target system, such as Slowloris and HTTP POST floods.
The most dangerous DDoS attack to date was the Mirai botnet attack in 2016. The Mirai botnet consisted of compromised IoT devices, such as cameras and routers, that were used to carry out massive DDoS attacks on several high-profile targets, including DNS provider Dyn. The attack caused widespread disruption and highlighted the vulnerabilities of IoT devices.
To mitigate the risk of DDoS attacks, organizations should take steps such as implementing a DDoS mitigation plan, using anti-DDoS services, and conducting regular vulnerability assessments. It’s also important to keep software and systems up-to-date and to have incident response plans in place to respond to attacks.
See more: AirAsia targeted by Daixin ransomware group losses valuable customer data
DDoS mitigation plans typically involve a combination of techniques, such as network filtering, traffic shaping, and rate limiting, to detect and block malicious traffic. Anti-DDoS services can also provide an additional layer of protection by monitoring traffic and blocking malicious requests.
See more: What is VPN – Difference between SSL VPN and IPSec VPN
In conclusion, DDoS attacks are a serious threat to organizations, and there are several types of attacks that attackers can use to overwhelm target systems. To mitigate the risk of DDoS attacks, organizations should implement a DDoS mitigation plan, use anti-DDoS services, and conduct regular vulnerability assessments.
We hope you found article interesting. For more exclusive content follow us on Facebook, Twitter and LinkedIn