Hackers Hide Backdoors beneath Harmful Self-Extracting Archives
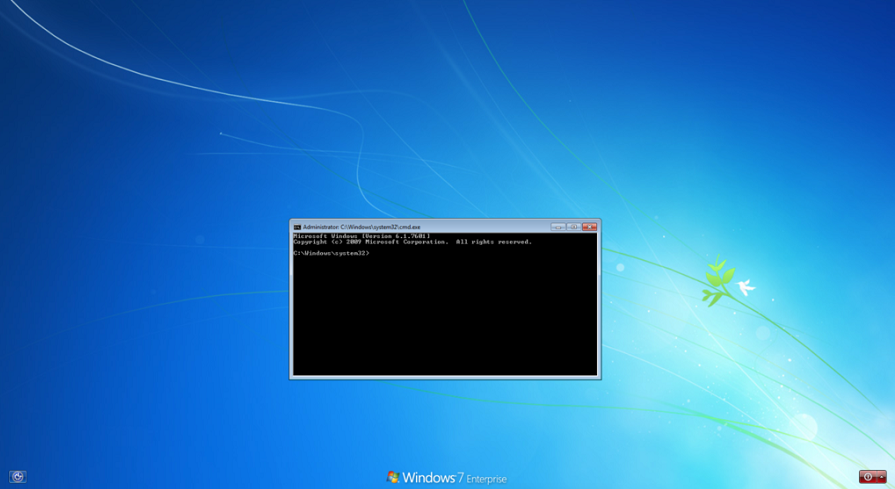
WinRAR self-extracting (SFX) archives include malicious functionality added by threat actors to covertly install persistent backdoors in target computers. These SFX files include bogus files that can start PowerShell, the command prompt, and the task manager with administrative rights.
Assaults using SFX files
Researchers from CrowdStrike claim that threat actors start by uploading a password-protected SFX file made with WinRAR or 7-Zip to the targeted system.
- They utilize stolen credentials to log into a system and attempt to take advantage of Utilities Manager, a legitimate Windows accessibility program (utilman[.]exe).
- The application is then configured to link a debugger (another executable) to a particular program in the Windows Registry. Every time the program is launched, the debugger will launch automatically.
- The SFX file that acts as a decoy and contains an empty text file is triggered by the utilman[.]exe. In order to open a backdoor on the system, the file is made to take advantage of WinRAR’s setup options to launch PowerShell, add additional commands, and build an SFX archive.
A seemingly empty SFX archive file can be disregarded by defenders and missed by technology-based detections. A persistent backdoor to a victim’s environment, however, could be made available to hackers if it is used in conjunction with a particular registry entry.
See more: Iranian hackers caught executing malicious attacks posing as Ransomware
Why did the attackers pick Utlman?
Threat actors can set up backdoors via the Image File Execution Options (IFEO) debugger in the Windows registry by abusing utilman[.]exe.
- Threat actors used the IFEO registry key to launch binaries of their choice on the target machine without being authenticated and to get around security safeguards.
- SFX files effortlessly decompress and show the file contents even if the target users don’t have decompression tools like WinRAR or 7-Zip.
See more: Massive leak exposes US deep involvement in Ukraine issue
Attackers can execute PowerShell and malicious scripts without activating the security agent by using modified SFX archives. Users are advised to pay close attention to SFX archives and use suitable unarchiving software or other tools to examine the content of the archive in order to prevent such attacks. Also, it is advised to search the SFX archives for any additional hidden features.
Author: Sayyam Gangwal
We hope you found article interesting. For more exclusive content follow us on Facebook, Twitter and LinkedIn






