Strelastealer malware targeting Outlook and Thunderbird users
Strelastealer malware is an information stealing malware which is actively targeting Outlook and Thunderbird users. This information stealing malware was initially discovered by analysts at DCSO CyTec in November and is targeting Spanish users. It specifically steals email account credentials from Outlook and Thunderbird unlike other info stealing malwares that steal data from cloud gaming apps, cryptocurrency wallets, browsers, and other data sources.
The modus operandi of this malware is that it sends email attachments to the targeted user. These attachments generally contain ISO files. ISO files refers to Optical Disk Image and acts as a achieved file comprising of data stored in optical disc, including its file system. ISO can easily be used to execute a malware by crafting it specially to exploit a vulnerability in the executable used to open the ZIP as Windows Explorer.exe. The payload inside can run any command using the access rights of the software.
See more: Vodafone Italy confirmed data breach after reseller compromised
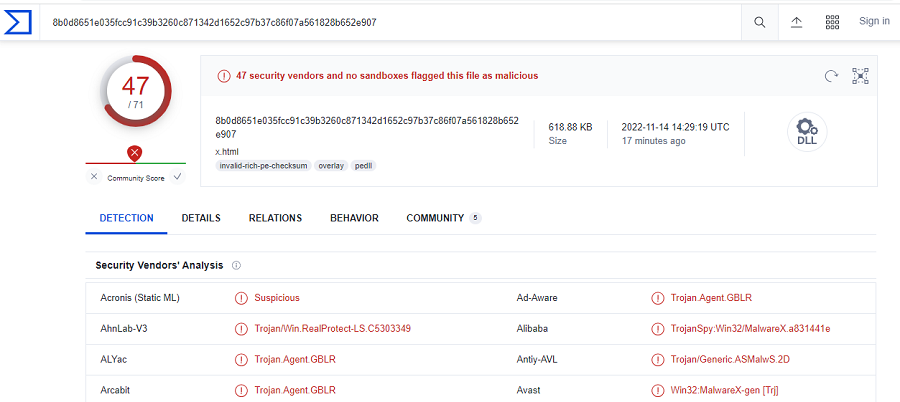
In some scenarios, the ISO contains a .lnk file (Factura.Ink) along with a HTML document which is a polyglot file (x.html). when the user opens an HTML file on a web browser, he will see a text document, and when it is opened via an executable, the payload is installed.
Once the payload is installed, the attacker then looks for login.json and key4.db in %APPDATA%\Thunderbird\Profiles\ directory for stealing account credentials. Outlook is targeted as the malware accesses the Windows Registry and tries to steals the software’s key, after which it inspects the IMAP details such as User, Password, and Server values. If found, the malware exfiltrates the content to a C2 server that is controlled by the attacker.
After this step, it waits for the attacker’s response. If response is received, then the malware quits. If there is delay in response or response is not received, it repeats the same routine after a 1-second sleep session.
See more: Thomson Reuters exposed TBs of sensitive data over internet
Outlook and Thunderbird are widely used mail platforms to send and receive emails however they also invite the attention of attackers as email attachments are the easiest way to deceive users. Users should keep below points in mind before opening any attachments that are shared over the email.
- Avoid opening attachments from unknown senders/sources.
- Always scan the attachments for the presence of any virus.
- Have a updated security system installed on the systems.
We hope you found article interesting. For more exclusive content follow us on Facebook, Twitter and LinkedIn






