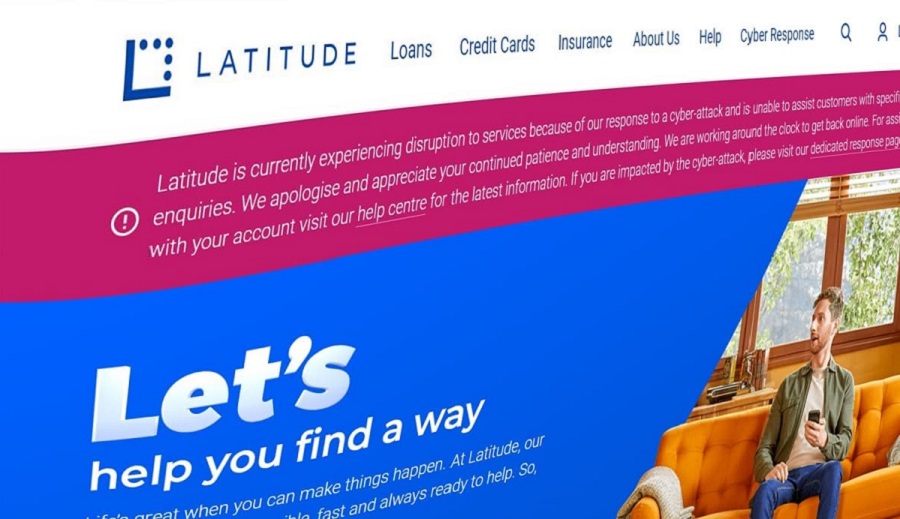
14 Million Customers Affected in Latitude Financial Data Breach
Latitude Financial, a financial services company based in Australia and New Zealand reported a data breach on March 16 after detecting unusual activity on its systems. The company initially believed that the breach had affected 328,000 customers with the majority of records being driver’s license numbers. On March 20, Latitude Financial revealed that the hack also involved the theft of copies of passports, passport numbers, and Medicare data.
Further investigation revealed that the breach was more extensive than initially believed. On March 22, the company reported that the breach had affected a “large-scale” number of customers and applicants across Australia and New Zealand, and on March 27, it was revealed that over 14 million customers had been affected.
The stolen data included customer names, dates of birth, addresses, and telephone numbers as well as 7.9 million driver’s license numbers, approximately 53,000 passport numbers and 100 monthly financial statements.
See more: Washington County Sheriff’s Office Hit by LockBit Ransomware
Latitude Financial has stated that it will directly contact all affected customers and reimburse those who choose to replace stolen ID documents. The Australian Federal Police is investigating the cyber-attack, and the company has engaged the help of the Australian Cyber Security Centre and external cybersecurity experts.
In addition to the investigation by authorities, Latitude Financial may also face legal action related to the breach. Two Australian law firms have announced that they are investigating potential legal action against the company including whether appropriate cybersecurity protections and protocols were in place and the circumstances surrounding the breach itself.
See more: Tiktok banned in EU amidst data privacy concerns
The breach highlights the ongoing threat of cyber-attacks and the importance of strong cybersecurity measures to protect sensitive customer data. Companies must remain vigilant in monitoring their systems for suspicious activity and take steps to secure their networks against malicious actors.
Author: Alok Kumar
We hope you found article interesting. For more exclusive content follow us on Facebook, Twitter and LinkedIn






