Cloud Computing: Risks, Challenges and Solution
Cloud computing has many benefits, but it also poses significant risks and challenges for cybersecurity. Some of the risks include data breaches, insecure interfaces and APIs, insider threats, and compliance issues. To mitigate these risks, businesses can implement solutions such as multi-factor authentication, encryption, regular security assessments, employee training, and cloud security services.
Best practices for cybersecurity in cloud computing include choosing a reputable provider, implementing a strong security policy, monitoring activity and logs, updating software, and having a disaster recovery plan. By understanding and addressing these risks and challenges, businesses can enjoy the benefits of cloud computing while keeping their data and systems secure.
As more businesses move their operations to the cloud, cybersecurity has become a critical concern. While cloud computing offers many benefits, it also poses significant risks and challenges for cybersecurity. We have explored the risks and challenges of cybersecurity in cloud computing and potential solutions to mitigate these risks.
1. Risks and Challenges of Cybersecurity in Cloud Computing
- Data breaches and unauthorized access
- Insecure interfaces and APIs
- Insider threats and human error
- Compliance and regulatory issues
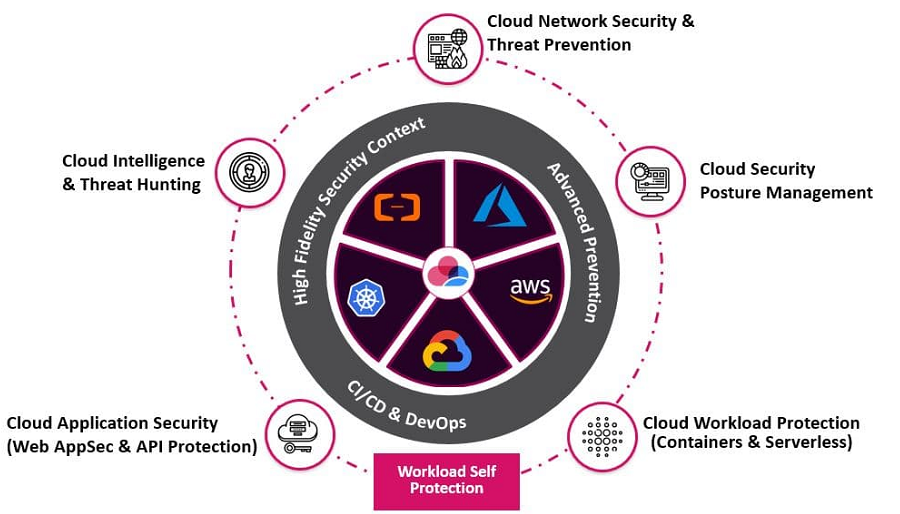
2. Solutions to Mitigate Risks and Challenges
- Multi-factor authentication and access controls
- Encryption and data protection
- Regular security assessments and audits
- Employee training and awareness programs
See more: Phases of Incident Response and Planning
3. Best Practices for Cybersecurity in Cloud Computing
- Choose a reputable cloud service provider
- Implement a strong security and compliance policy
- Monitor and analyse cloud activity and logs
- Implement a disaster recovery plan
See more: Apple releases security update for Older iOS and iPadOS Models
As cloud computing continues to transform the way businesses operate, cybersecurity must be a top priority. By understanding the risks and challenges of cloud computing and implementing best practices and solutions, businesses can protect their data and systems in the cloud.
Author: Utkarsh Mathur
We hope you found article interesting. For more exclusive content follow us on Facebook, Twitter and LinkedIn