Kingfisher insurance falls victim to Lockbit 3.0 ransomware
UK based insurance company Kingfisher has become latest target of ransomware gang LockBit 3.0. The gang has confirmed about this breach in a latest dark web post. As per the reports, this ransomware group claims to have stolen approx 1.4 TB of data from the company which includes the personal data of employees and customers.
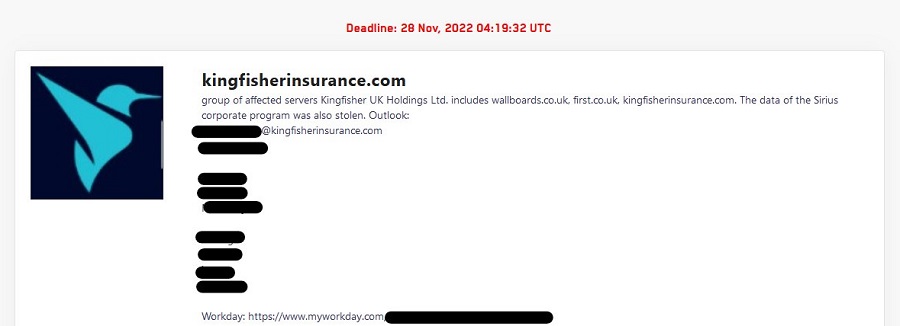
This gang has provided a deadline till 28th November to fulfil its demands and in case if the company fails to adhere their demand, they will be publishing the stolen data to the public. Kingfisher joins the list to be the sixth company of this month to be targeted by this group. The company has confirmed about the breach however they have denied about the size of data breached.
According to the Kingfisher’s statement:
IT team has blocked all external access and isolated the servers as soon as they received notification about the security incident. The company has conducted further investigation and concluded that there was “no ongoing impact on its business operations.”
LockBit has been targeting critical infrastructure such as health, energy, transport & other sectors. This threat vector has been active and operating since 2019. It is one of the most popular and dangerous ransomwares that has been targeting different sectors.
Recently Japanese tech firm Oomiya has also been hit by LockBit 3.0 and it is believed that multiple supply chains have been impacted due to this attack.

Lockbit 3.0 generally forms various threads to execute multiple tasks simultaneously in order to minimize the time involved in data encryption. Post the encryption, victim’s desktop wallpaper displays the below message.
All your important files are stolen and encrypted! You must find HLJKNskOq.README.txt file and follow the instruction!
This new and advanced version of Lockbit is more faster than the previous versions. It comes with a mechanism of disabling Windows Defender and allows to temper Windows logs. Another interesting fact is that this gang has released a bug bounty program. It also encourages researchers to discover and submit security reports for reward money.
See more : Another security breach surfaced- This time it is Policybazaar
There are several measures to protect or reduce the risk of this ransomware by enabling 2MFA and by providing a strong password that is complex in nature and not easily guessable. Endpoint services such as EDR & AV should be in place and unnecessary access should be removed.
Follow on Facebook: Latest Hacking Updates






