Mirai Botnet exploits TP-Link to Expand Its DDoS Army
The world was introduced to the deadly capabilities of the Mirai botnet in 2016. This virus infected thousands of IoT (Internet of Things) devices, including routers, cameras, and DVRs, transforming them into a huge network of zombies capable of launching DDoS (Distributed Denial of Service) assaults. Mirai versions have been identified since then, each with its own set of capabilities and targets.
A new strain of the Mirai botnet targeting TP-Link routers was spotted recently. This variation infects the router and adds it to the botnet’s army of DDoS devices by exploiting a vulnerability in the router’s firmware. This paper will investigate this new Mirai strain and the ramifications it may have for the security of the IoT ecosystem.
The Mirai variant’s TP-Link vulnerability is linked to a backdoor in the firmware. An attacker can get access to the device by exploiting this backdoor, which was meant to let TP-Link support workers to remotely access the router. Once access is gained, the attacker may install Mirai botnet software on the router and add it to the botnet’s army of zombie devices.
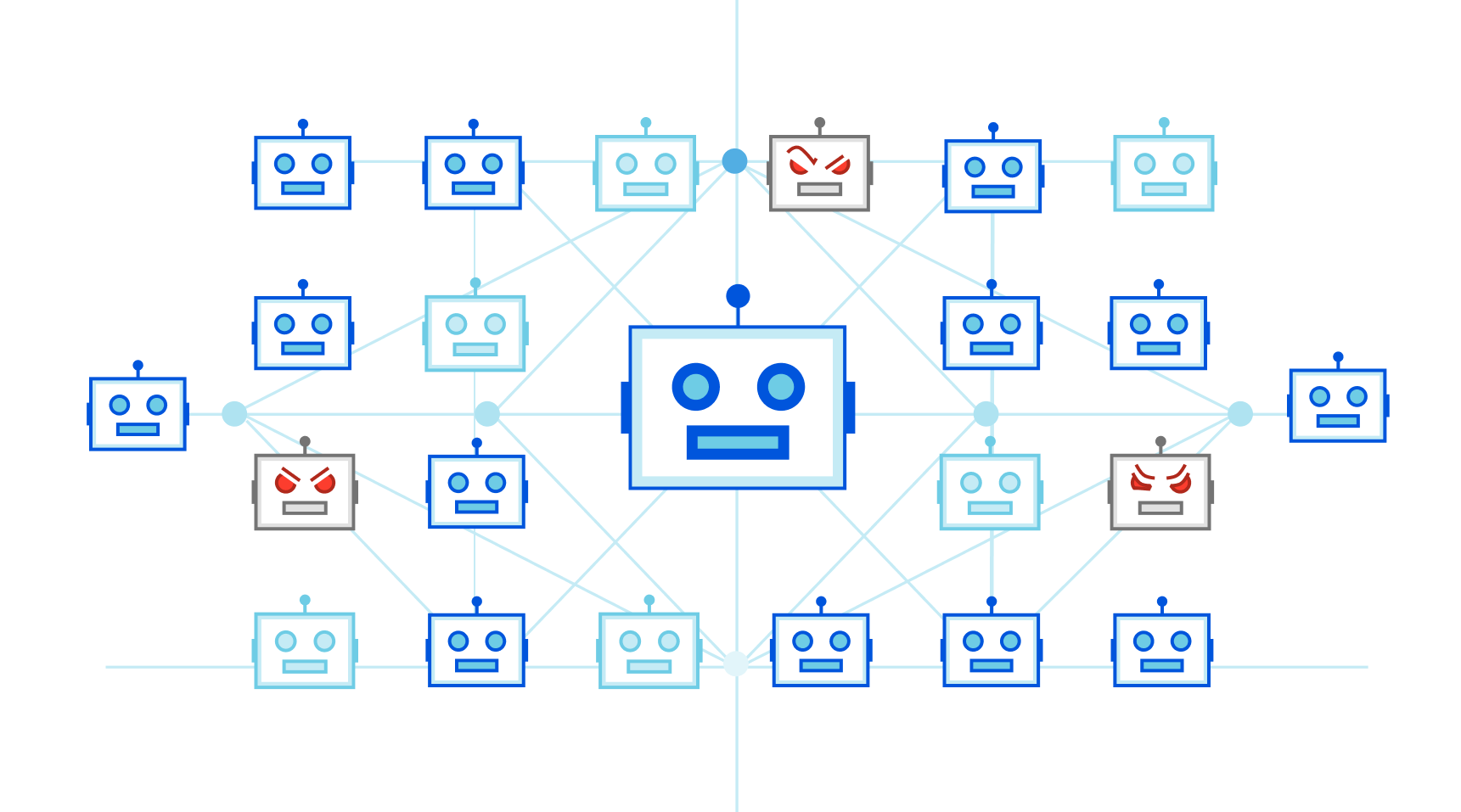
The Mirai botnet is well-known for its capacity to perform enormous DDoS assaults that may bring even the most durable networks to a halt. The botnet’s army of zombie devices may overload a targeted network, making genuine traffic impossible to reach its goal. This can result in substantial interruption and downtime, as well as financial losses and reputational harm.
The TP-Link vulnerability used by the Mirai version is simply one of several security flaws in the IoT ecosystem. Many IoT devices are designed with ease of use and low cost in mind, rather than security. As a result, many Internets of Things devices are inherently unsecure and prone to attack.
See more: BlueNoroff Launches RustBucket Malware Against Mac Users
It is critical to adopt security best practises to reduce the dangers posed by IoT devices. This involves changing firmware and passwords on a regular basis, eliminating unneeded capabilities and ports, and employing robust encryption. It is also critical to understand the security threats connected with IoT devices and to take precautions to safeguard your network and devices.
See more: FIN7 Hackers Caught Exploiting Veeam Vulnerability
The discovery of this new Mirai version aimed against TP-Link routers serves as a clear warning of the security concerns connected with IoT devices. It emphasises the need of manufacturers prioritising security in their goods and users taking precautions to protect themselves and their networks. As the Internet of Things ecosystem grows and evolves, it is critical that we adopt a proactive approach to security to guarantee that the advantages of new technologies are not exceeded by the hazards.
Author: Priyanka Priyadarshini Dwibedy
We hope you found article interesting. For more exclusive content follow us on Facebook, Twitter and LinkedIn






