Python-based Legion hacking tool targeting websites & web services
Legion is a popular python-based hacking tool designed for targeting websites and web services. It is a powerful and flexible tool that can be used for a variety of purposes, including penetration testing, vulnerability scanning, and network reconnaissance.
The program was created by the security company BlackArch and is freely downloadable. With a simple user interface that makes it simple to operate, users may launch attacks swiftly and effectively.
A number of features and functionalities are available with Legion, such as the capacity to do automated vulnerability checks and conduct brute-force assaults and password cracking. Additionally, it has modules for scouting out target networks, spotting potential flaws, and exploiting them.
See more: Hacktivist Indonesia claims to have attacked 12k Indian websites
The capability of Legion to launch attacks on web applications is one of its primary characteristics. The program supports a number of attack methods, such as remote file inclusion, SQL injection, and cross-site scripting (XSS). It also has a web application scanner that can find and use vulnerabilities in target applications automatically.
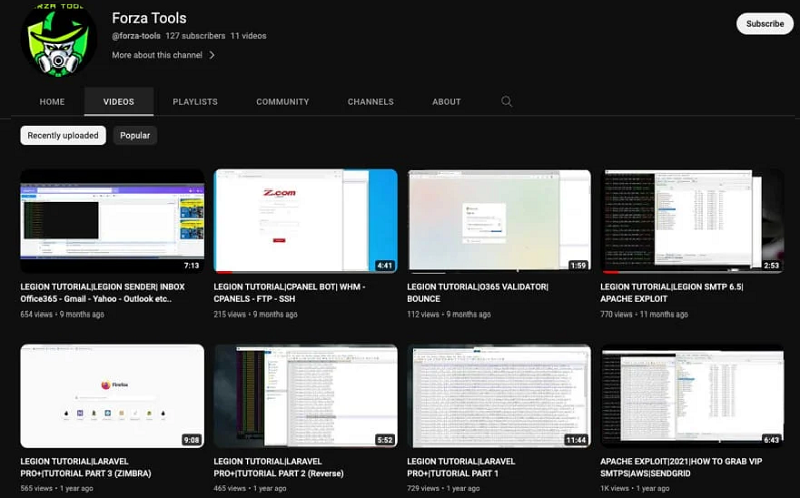
Legion’s capacity to carry out password attacks is yet another essential capability. The program can break passwords using a number of techniques, such as brute-force, dictionary, and hybrid attacks. Additionally, it allows for the usage of unique password dictionaries, which makes it simpler to break complex passwords.
See more: Massive iPhone Breach: QuaDream’s KingsPawn Spyware Unleashed on Devices
Legion has a variety of plugins and modules in addition to its main capabilities that can be used to expand its capability. These comprise tools for executing social engineering attacks, doing network reconnaissance, and finding weaknesses in targets’ systems.
Overall, Legion is an effective and adaptable hacking tool that can be applied to a variety of tasks. For security experts and penetration testers who must find and take advantage of weaknesses in target systems, it is the perfect tool. However, it should be underlined that users should always secure the necessary permissions and authorizations before utilizing the tool, and that it should only be used in a morally and legally acceptable manner.
Author: Priyanka Priyadarshini Dwibedy
We hope you found article interesting. For more exclusive content follow us on Facebook, Twitter and LinkedIn






