Secrets of building strong SOC team: Challenges and Solutions
The SOC team, sometimes also called Blue-team is the first line of defense and is responsible for protecting organizations against cyberattacks. Being part of the SOC team, it is individual’s responsibility to effectively manage security incidents such as Investigating Potential Incidents, Prioritizing Detected Incidents, Responding to Incidents, and Reporting to the Management, etc.
Any organization having internal SOC solutions must ensure that the team has adequate technical understanding, tools availability, etc. In case any of the SOC team members are not trained enough or tools are unavailable/not configured properly, it might raise a security alarm and put the organization at risk.
Most of the time, SOC’s responsibilities exceed their capacity. In such cases, some of the common challenges that SOC encounters are:
Hiring Critical Roles
There is a substantial skills gap in the cybersecurity sector. Because of this, it is challenging for businesses to find and keep the skills they need to defend against cyber-attacks.
Ruling Out False Positives
The typical SOC receives tens of thousands of notifications per day, but only a small percentage of them are genuine threats. SOC analysts spend significant time and resources searching through the bulk of logs for real threats.
Operational Noise
Every organization may have to allow/whitelist some processes which might carry risk however required for business continuity.
Team size
Most of the time, a CISO or CTO has budget limitations due to which they do neck-to-neck hiring of resources for 24*7 operations. Sometimes when one employee has to take leave others have to extend duties.
Considering the above challenges, Latest Hacking Updates tries to explain the key components which should be kept in mind while implementing strong SOC/SIEM solutions.
1: Decide the team size as per scope
Normally a SOC team consists of 3 roles which include Security analyst, Threat hunter, and Manager/Leads. The ratio of team should be 6:3:1 i.e. for 6 Security analysts, there should be 3 Threat hunters(one in each shift) and one technical lead reporting to manager.
Security analyst They are first responders and reports on cyber threats and implement any changes needed to protect the organization. The initial responsibility of Security analysts is to investigate the alert, raise incidents and get closure.
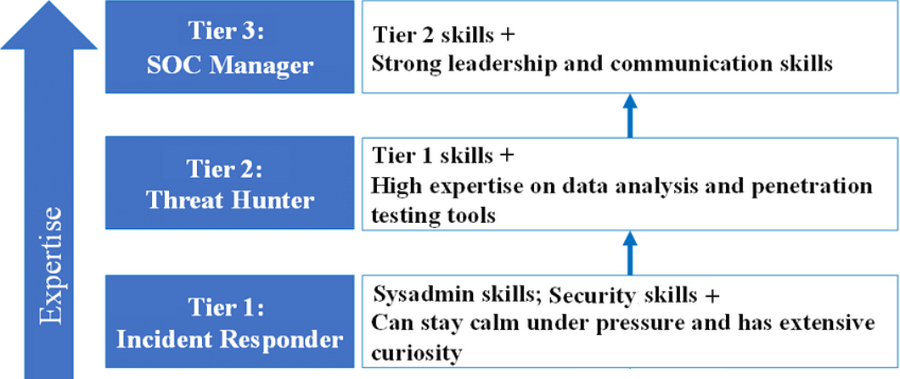
Threat hunter Threat hunters are also called threat analysts or security analysts. They usually come into the picture when a true positive incident is reported and needs investigation from a threat/risk perspective. They are also responsible for preparing RCA and other documentation that other teams/stakeholders might need.
Manager/Lead SOC manager role includes hiring and training the resources. Preparing policies and process documents. They also administer the SIEM tool from a configuration perspective.
2: Automate as much as possible:
A combination of security automation along with security analysis helps identify more incidents and protect against malicious incidents.
3: Effective SIEM and other solutions
The abilities of the SOC team mostly depend on its technology capabilities. SIEM tool along with MDR/EDR solution should collect and aggregate data, prevent malicious threats, and respond to the threats detected. Behavior-based SIEM and EDR solutions are considered as best solutions if configured properly and get enough time to understand organizational behavior.
4: Understanding of latest vulnerabilities and threats
Threat intelligence data from external sources, such as IOCs, latest published CVEs, CWEs, threat briefing reports, etc provides insight into the latest risk/threats to the organization. Understanding this threat intelligence helps the SOC team defend effectively.
5: Ensure coverage
A key responsibility of a SOC Manager/team is to understand the scope and ensure that the scope is covered for any suspicious alerts. This includes the understanding of the organization network, types of OS/applications used, intrusion prevention (IPS), and detection (IDS) systems deployed across the organization.
6: Roles and responsibilities
In order to run effective SOC, it is necessary that the team members are aware of their roles & responsibilities and encouraged by the manager to ensure the deliverables expected from them.
7: Training and certification
SOC team should be encouraged to go through various training programs to enhance skills. These programs/training include OWASP top 10, SANS 25, Certified Hacking and forensics Investigator, Cloud security Malware analysis, etc., and are offered by many organizations.
Even though it might look like the SOC team is functioning smoothly however it is management’s responsibility to measure the performance of SOC teams for continuous improvement. This can be done by asking for monthly/weekly dashboards, mean time to detect and mean time to respond, total incidents vs false positives vs operational noise, analyst’s productivity, etc.
See more: What Everyone Must Know About BLOCKCHAIN
See more: What to prefer for web application security – RASP or WAF
We hope you found article interesting. For more exclusive content follow us on Facebook, Twitter and LinkedIn






