CISA Warns Industrial Control Systems have critical Vulnerabilities
On Tuesday, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) issued eight Industrial Control Systems (ICS) advisories highlighting serious vulnerabilities impacting products from Rockwell Automation and Delta Electronics.
These include three bugs in the software developed by ETIC Telecom, including one that results from the Remote Access Server’s (RAS) web portal’s failure to confirm the authenticity of the firmware, a directory traversal error in the RAS API and a file upload problem.
According to CISA, successful exploitation of these flaws could give an unauthenticated attacker access to files and credentials, grant them more privileges, and enable them to remotely run arbitrary code.
Based on evidence of ongoing exploitation, CISA has added three new vulnerabilities to its Known Exploited Vulnerabilities Catalog.
- CVE-2023-23397 Elevation of Privilege Vulnerability in Microsoft Outlook
- CVE-2023-24880 Vulnerability in Microsoft Windows SmartScreen Security Feature
- CVE-2022-41328 FortiOS Path Traversal Vulnerability for Fortinet
The most serious flaw on the list is CVE-2023-1133 (CVSS rating: 9.8), which is caused by the fact that InfraSuite Device Master accepts unauthenticated UDP packets and deserializes the data, enabling an unauthenticated remote attacker to run arbitrary code.
See more: New NAPLISTENER Malware used by REF2924 to avoid network detection
The CISA issued a warning about two additional deserialization flaws, CVE-2023-1139 (CVSS score: 8.8) and CVE-2023-1145 (CVSS score: 7.8), which could be used as a weapon to acquire remote code execution.
Even worse, the adversary might use CVE-2023-28755 as a weapon to replace current executable files with trojanized versions, which could result in remote code execution. Successful exploitation of these flaws could enable an attacker to possibly execute remote code on the target system or device or cause the software to crash, according to CISA.
A high-severity buffer overflow vulnerability in Rockwell Automation ThinManager ThinServer (CVE-2022-38742, CVSS score: 8.1) that could allow unrestricted remote code execution has now been publicly disclosed, more than six months after CISA first made the vulnerability known.
See more: Karnataka Remote Sensing Applications Centre hacked by Lockbit
Users are advised to update their devices as mitigation steps and suggests a number of workarounds:
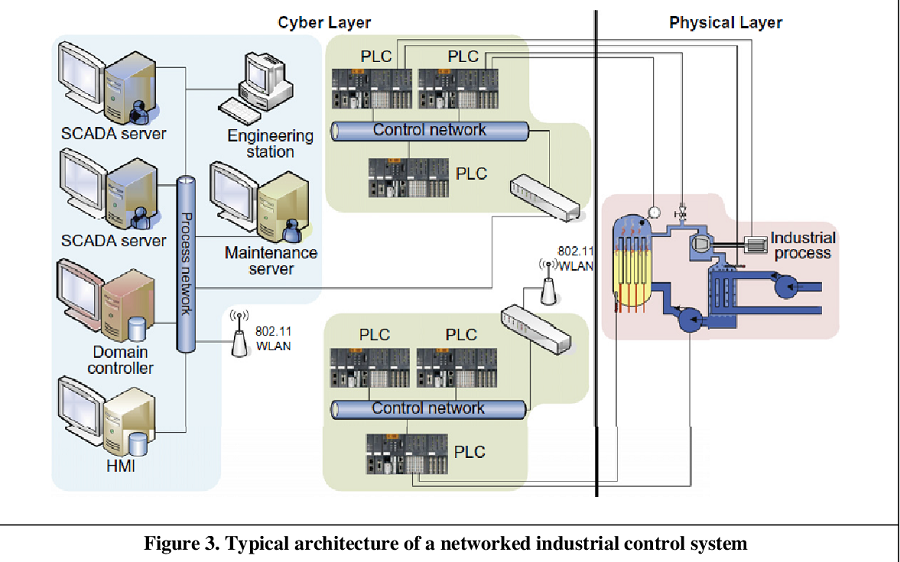
- All control system devices should have as little network exposure as possible, and the should not be available via the internet.
- Place control systems and external devices behind firewalls to isolate them from corporate networks.
- Manually resetting the database password is recommended for CVE-2022-45444.
Author: Vaishnavi Priyanka and Sanghamitra
We hope you found article interesting. For more exclusive content follow us on Facebook, Twitter and LinkedIn