DotRunpeX malware delivering malware families via malicious ads
Numerous well-known malware families, including Agent Tesla, Ave Maria, BitRAT, FormBook, LokiBot, NetWire, Raccoon Stealer, RedLine Stealer, Remcos, Rhadamanthys, and Vidar, are being distributed using a new piece of malware dubbed dotRunpeX.
DotRunpeX is a brand-new injector that uses the Process Hollowing technique and was written in .NET to infect systems with a variety of recognized malware families.
DotRunpeX, which is currently under development, enters the infection chain as second-stage malware and is frequently spread through phishing emails as malicious attachments via a downloader (also known as a loader).
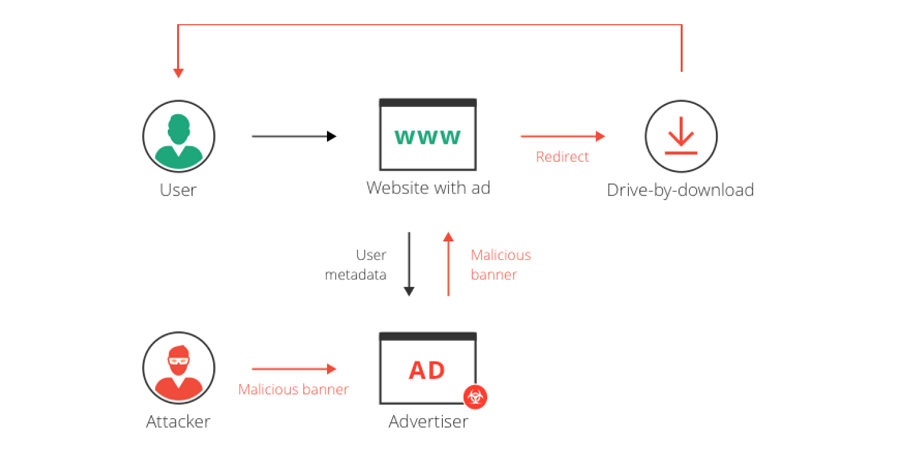
As an alternative, it has been known to use malicious Google Ads on search result pages to steer unwary users searching for popular software like AnyDesk and LastPass to imitation websites hosting trojanized installers.
See more: Go-Based Hinata Bot Abuses Vulnerabilities for DDoS Attacks
The most recent DotRunpeX artefacts, which were discovered in October 2022, use the KoiVM virtualizing protector to add an additional layer of obfuscation.
Defeating #dotRunpeX — New #virtualized .NET injector abusing advanced techniques to deliver numerous malware families.
CP<r> provides an in-depth analysis of this threat introducing several PoC techniques for reversing protected/virtualized #dotnet code. https://t.co/PxzqoIJJKu— Check Point Research (@_CPResearch_) March 15, 2023
According to a security firm Checkpoint analysis, each dotRunpeX sample contains a malware family’s embedded payload that is intended to be injected, and the injector also specifies a list of anti-malware processes that should be terminated. In turn, this is made possible by exploiting a weak process explorer driver (procexp.sys) built into dotRunpeX to gain kernel mode execution.
See more: The Growing Threat of Cyber Attacks on EV Charging Stations
Based on the language references in the code, there are indications that dotRunpeX may be connected to actors who speak Russian. The emerging threat primarily distributes the RedLine, Raccoon, Vidar, Agent Tesla, and FormBook malware families.
Author: Sarthak Murtadak and Priyanka Sonawane
We hope you found article interesting. For more exclusive content follow us on Facebook, Twitter and LinkedIn