Emotet Malware Spreads via Microsoft OneNote
After a three-month hiatus, Emotet virus is back and utilizes Microsoft OneNote files to get beyond macro-based protection measures. Gold, a malicious actor that is responsible for running Emotet is either Crestwood, Mummy Spider, or TA542.
The malicious actors attempted to spread the virus through Word and Excel documents. Nevertheless, only a small number of users risked infection because Microsoft now disables macros by default for that type of file. Thus, hackers are increasingly utilizing Microsoft OneNote files.
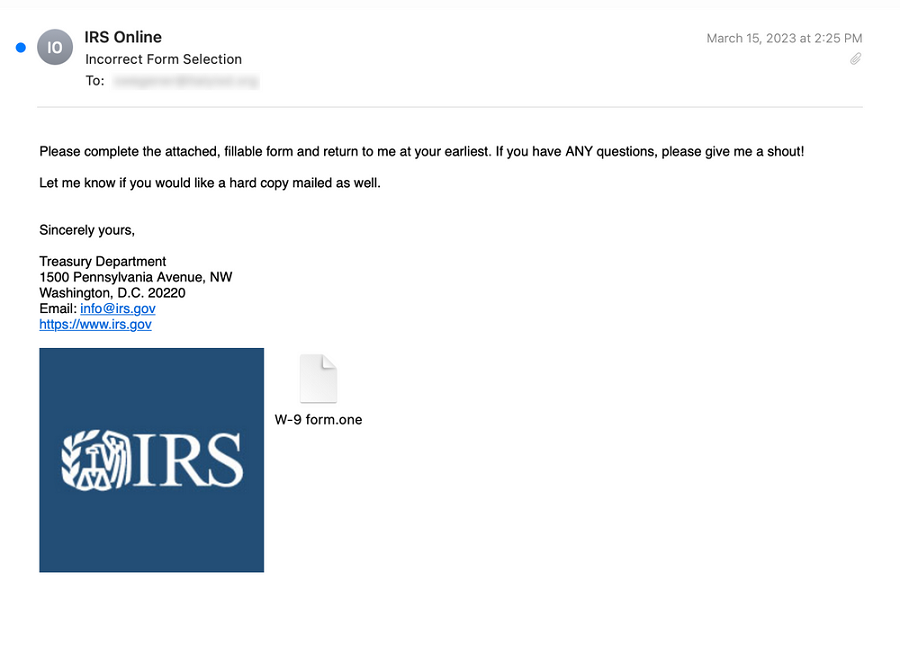
Malicious attachments are often transmitted by the dropper virus through spam emails. OneNote attachments were the next best option once Microsoft chose to restrict macros in downloaded Word files.

Hackers attach Microsoft OneNote documents to emails with a message stating that the document is secured and instructing the user to double-click the “View” button in order to see the document correctly.
Threat actors concealed a malicious VBScript file called “click.wsf” inside the “View” button in order to accomplish their objectives. A DLL is downloaded and run from a likely compromised website via the file’s obfuscated script.
See more: DotRunpeX malware delivering malware families via malicious ads
Microsoft OneNote always shows a warning notice when a user tries to open an embedded file. The majority of users, however, just click “OK” to dismiss the message and continue with their work.
In this scenario, the embedded click happens just after the user clicks the OK button.
WScript.exe is launched from OneNote’s Temp folder to execute the wsf VBScript file. The script puts the Emotet malware as a DLL [VirusTotal] in the same Temp folder and installs it there. Launching the DLL using regsvr32.exe is the next procedure.
What could be at risk?
Emotet successfully deploys and then takes contacts and email content. It can then get guidance from the command-and-control server.
Cobalt Strike and other viruses are typically also installed. They provide Emotet hackers with the ability to gain illegal access to the device and use it as a launchpad to extend their network-wide proliferation.
See more: Russian hacktivists steal data after hacking STALKER 2 creator
How to Stop Adversary from accessing Documents for Microsoft OneNote?
OneNote files are used by other malware campaigns besides Emotet. Windows administrators are recommended to set group policies such that any of the following is true until Microsoft is able to provide specific anti-phishing protection:
Microsoft OneNote may either prohibit all embedded files or allow users to choose certain file extensions that should be blocked from executing.
Author: Komal Gaware and Vaishnavi Bhujbal
We hope you found article interesting. For more exclusive content follow us on Facebook, Twitter and LinkedIn






