Fake Telegram and WhatsApp targeting Windows & Android Users
Researchers at ESET have discovered numerous fraudulent websites that are imitating messaging apps like Telegram and Whatsapp. Using trojanized versions of these instant messaging services, several phony Telegram and WhatsApp websites have been discovered, particularly focusing on Android and Windows users. It’s noteworthy that the bulk of the dangerous applications that researchers discovered are clippers, a category of malware that takes or modifies the contents of the clipboard.
How was it disseminated?
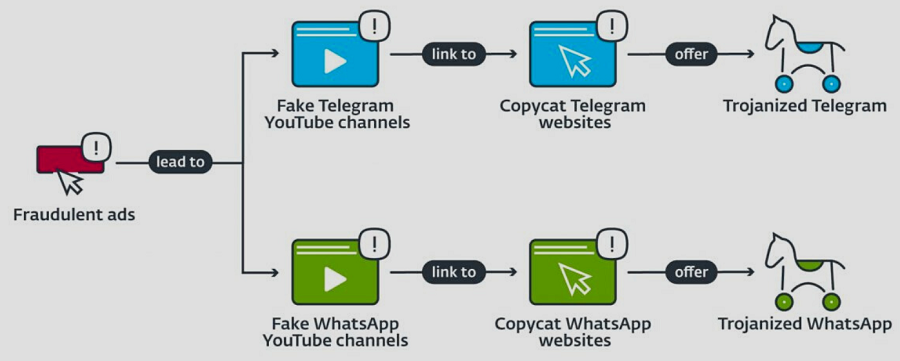
They are mostly marketed by their operators to clients who speak Mandarin. Before redirecting users to phoney Telegram and WhatsApp websites, the threat actors first develop Google Ads that target viewers to phoney YouTube channels.
According to researchers, the fraudulent websites offer Telegram and WhatsApp download links for every supported operating system. Nevertheless, all links for Linux and Mac OS as well as the bulk of links for iOS point to the individual application’s official websites.
See more: NBA warns supporters of a data breach that exposed personal data
Android malware
The main objective of the trojanized Android applications is to eavesdrop on victims’ chat discussions in order to either swap any cryptocurrency wallet addresses with the attackers or exfiltrate sensitive data that would enable the attackers to steal cryptocurrency cash from the victims.
Windows malware
According to researchers, the Windows versions contain both cutters and remote access trojans. The RATs have a wider variety of malicious capabilities, including the ability to delete files and take screenshots, whereas clippers mostly target crypto-stealing.
Some of them can change the clipboard, which gives them the opportunity to hijack bitcoin wallets. The Windows applications were hosted on the same domains as the Android versions.
Remote access malware
With the aid of the numerous modules they include, the threat actors are able to do tasks including stealing clipboard data, recording keystrokes, searching the Windows Registry, capturing the screen, obtaining system information, and managing files.With one exception, every remote access trojan we examined was based on the renowned Gh0st RAT, malware that is commonly utilised by cybercriminals owing to its open availability, according to researchers.
See more: Go-Based Hinata Bot Abuses Vulnerabilities for DDoS Attacks
In order to steal bitcoin from their victims, threat actors utilise the Android and Windows apps Telegram and WhatsApp, which have been infected by trojans.
Author: Twinkle Sahoo
We hope you found article interesting. For more exclusive content follow us on Facebook, Twitter and LinkedIn






