Github replaces RSA SSH host key after public exposure
In order to secure Git operations, Github has replaced the vulnerable RSA SSH Host key. This action was taken in order to keep the security measures in place as the cloud based repository service was earlier exposed in a public repository.
The action, which was taken at 05:00 UTC on March 24, 2023, is said to have been done as a precaution to stop the malicious parties from pretending to be the service or listening in on users’ SSH operations.
At approximately 05:00 UTC on March 24, out of an abundance of caution, we replaced our RSA SSH host key for https://t.co/0iKPk2k19C. Read more here: https://t.co/tuXsZ9Am9u
— GitHub Security (@GitHubSecurity) March 24, 2023
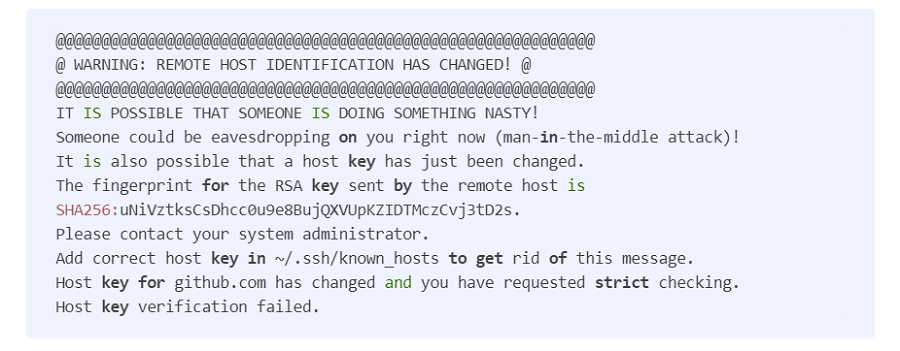
Users using ECDSA (Elliptic Curve Digital Signature Algorithm) or Ed25519 credentials have not been impacted. However, if you receive a warning notice when attempting to connect to GitHub.com via SSH, take the recommended actions to delete the previous key and add the new one. Users of GitHub Actions should be aware of potentially unsuccessful workflow runs and change their workflows as necessary:
There is no proof, according to the Microsoft-owned business, that adversaries exploited the exposed SSH private key.
The issue was not caused by a breach of any GitHub networks or customer data. It has blamed the “accidental publication of private information” for it.
See more: Redline Info-stealer spread through Document signing providers
Hanley has analyzed and confirmed that the exposed RSA key in issue does not provide access to GitHub’s infrastructure or user data.
This change only applies to SSH-based Git operations that use RSA encryption. Additionally, GitHub.com web traffic and HTTPS Git operations remain unaffected.
It also mentioned that users of GitHub Actions who use actions/checkout with the ssh-key choice might experience failed workflow runs, and it added that it was in the process of updating the action across all tags.
See more: WooCommerce Payment Plugin vulnerability Fixed for WordPress
The revelation follows GitHub’s nearly two-month-old admission that unidentified threat players had obtained encrypted code signing certificates for some GitHub Desktop for Mac and Atom app versions.
Several documents and software projects, including those by GitHub, continue to use the SSH fingerprint of its now-revoked key despite the fact that GitHub has altered the private SSH keys:
Users should therefore add GitHub’s new key fingerprint to their /.ssh/known_hosts file in order to avoid receiving security alerts when establishing SSH sessions. Users should check that the fingerprint displayed on their screen matches the one for GitHub.com’s most recent key when they receive such alerts.
Author: Vaishnavi Bhujbal
We hope you found article interesting. For more exclusive content follow us on Facebook, Twitter and LinkedIn






