How to detect hardware trojans in microchips
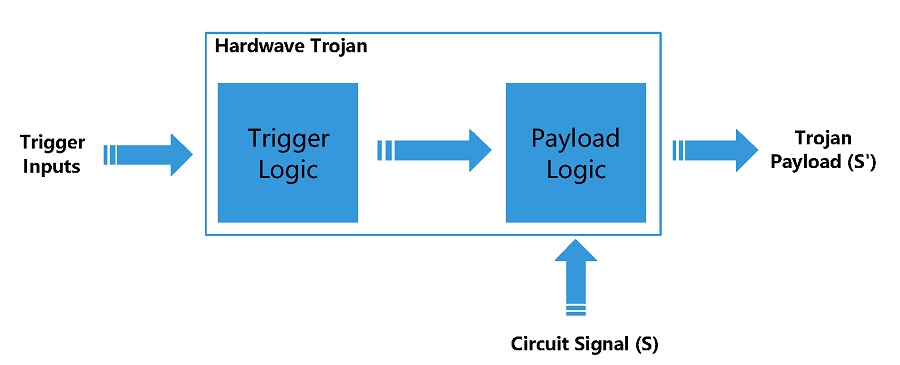
Security flaws can be found not only in software but can also be embedded in hardware, making technological applications vulnerable to a wide range of attacks.
To counteract these hardware Trojans, researchers are developing cutting-edge detection methods. By comparing chip blueprints with electron microscope images of the actual chips, their sophisticated system can spot discrepancies. In 37 out of 40 cases, this ground-breaking strategy was successful in identifying anomalies.
All chip photos, design data, and analysis techniques have been freely accessible online by the research team so that other researchers can access and use these materials for their own studies and improvements in the area.
Manufacturing facilities could be a hardware Trojan’s point of entry
Electronic chips are now used in a wide variety of products. They are typically created by businesses without their own manufacturing facilities. In order to produce the construction designs, highly specialized chip factories are contacted.
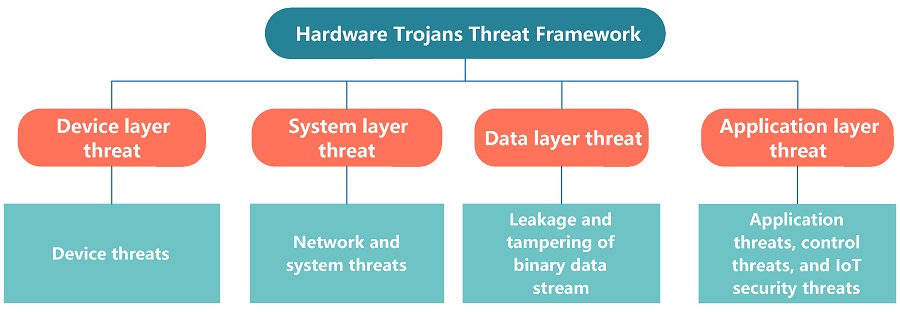
It’s possible that microscopic changes might be incorporated into the designs in the factories shortly before production that could override the security of the chips, and provides an illustration of the potential outcomes: Such hardware Trojans might enable an attacker to cripple portions of the communications infrastructure at the click of a button in extreme scenarios.
See more: Fake Telegram and WhatsApp targeting Windows & Android Users
The design files and the produced chips were available to the researchers. They could not, of course, add hardware Trojans to the chips after the fact. So, they used a ruse and altered the drawings retroactively rather than modifying the chips to ensure that there were little differences between the construction plans and the chips. The researchers next ran tests to see if they could see these changes without being aware of exactly where and what to look for.
The first phase required the researchers to prepare the chips using intricate mechanical and chemical procedures so that they could use a scanning electron microscope to obtain thousands of photos of the chip’s base layers. Many hundred thousand so-called standard cells, which perform logical operations, are included in these levels.
It was difficult to compare the chip photos and the building blueprints since we had to carefully superimpose the data first, explains Endres Puschner. Furthermore, every minor imperfection on the chip has the potential to obscure some of the image. A single particle of dust or a hair can cover an entire row of standard cells on the tiniest chip, which is 28 nanometers in size, the author writes.
See more: Cybercrime and its financial impact on Business
Almost all manipulations have been discovered
In order to properly compare standard cell for standard cell, the researchers used image processing techniques. They also looked for discrepancies between the construction blueprints and the microscopic images of the chips. “The results give cause for cautious optimism,” as Puschner sums up the findings. The researchers successfully identified every alteration for chips with diameters of 90, 65, and 40 nanometers. 500 false-positive results, or standard cells that were falsely labeled as transformed but were actually unaltered, were obtained. This is a very good rate, according to Puschner, who estimates that about 1.5 million standard cells were evaluated. The only chip the researchers could not detect three-minute changes in was the smallest one, measuring 28 nanometers.
Increased detection rate thanks to cleaner environments and improved algorithms
This issue might be resolved in the future with the greater recording quality. Additionally, employing them in a clean environment where contamination can be avoided will improve the rate of detection even more.
Author: Sayyam Gangwal
We hope you found article interesting. For more exclusive content follow us on Facebook, Twitter and LinkedIn