Lockbit adds Fullerton India Credit Company to victim list
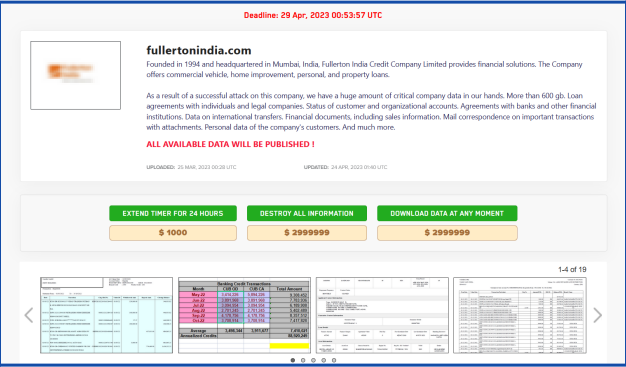
On 24 April 2023, LockBIT3.0 claimed to have added Fullerton India to its victim list. Fullerton India is a credit company which provides financial solutions. The group mentions publishing the entire collected data for free on their PR site if the ransom is not paid by 29 April 2023. Recent targets of the group include – SRF, Piramal Group, Laxmi organics, KSRSAC Karnataka, etc.
The actor mentioned in the post that the 600GBs of following information has been leaked which included loan agreements with individuals and legal companies, status of customer and organizational accounts, agreements with banks and other financial institutions, data on international transfers, financial documents, including sales information, mail correspondence on important transactions with attachments, personal data of the company’s customers.
The shared samples contains Account statements likely from loan applicants, Documents with Loan details, Consumer CIR – Cibil reports, Aadhar cards, Loan sanction documents, mortgage loan application form, statement of Income / ITRs, auto debit forms Timeline of the incident
On 24 April 2023, Lockbit group made the post public on its PR Site. 3. In the image we can see, the post was actually created on 25 March 2023, 2 days before the news was shared with the sensitive source and around 1 month before the post was made public. The group gives a 5 day deadline 29 April 2023 for anyone from the public and Fullerton to Destroy or Download the data for USD 3 Million.
LockBIT was previously known as ABCD ransomware and belonged to the Maze ransomware cartel. LockBIT started its independent activity in September 2019. After being independent of the cartel, the ransomware group instead of rebranding itself decided to release a new version and brand under the name of LockBIT 2.0 in June 2021.
See more: Play Ransomware Group Adds New Tools to Harvest More Data
LockBIT 2.0 grew in popularity and became one of the most recognized RaaS in 2021 and has surged in popularity again in the first quarter of 2022. According to leak site data analytics, 46% of all leak data provided by ransomware in the first quarter of 2022 was by LockBIT 2.0. This major impact made LockBIT 2.0 the most impactful RaaS for five consecutive months since its initial launch.
See more: Goldoson Android malware affects 60 apps with 100M installs
LockBIT 3.0 officially launched on 27 June 2022 and has brought some major changes to the ransomware. The beta version of LockBIT 3.0 was mentioned in a post on March 30, 2022, for hiring web pentesters on the dark web. LockBIT 3.0 also has 9 mirror Blogs, 24 mirror Servers with Backups and Direct inks, and 9 Chats reserve mirrors. Pricing Models.
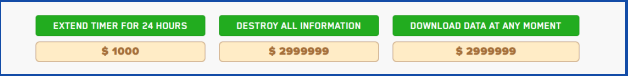
LockBIT 3.0 has a new extortion model. In this model, they have put three different pricing models for the leaked/compromised company’s data. First pricing model is “Extend TIMER FOR 24 HOURS”, the second pricing model is “DESTROY ALL DATA”, and the third pricing model is “DOWNLOAD DATA AT ANY MOMENT”. The pricing models are not just available for the company whose data is hacked and leaked, instead, anyone can pay and perform the action. This model is used to put more pressure on the targeted company.
We hope you found article interesting. For more exclusive content follow us on Facebook, Twitter and LinkedIn