New Cryptojacking Targeting Kubernetes Clusters for Dero Mining
From the beginning of February 2023, cybersecurity experts have uncovered the first-ever illegal cryptocurrency mining operation used to produce Dero.
According to CrowdStrike, the innovative Dero cryptojacking operation focuses on finding Kubernetes clusters that have anonymous access enabled on a Kubernetes API and are listening on non-standard ports that are accessible from the internet.
The change is a noticeable departure from Monero, which is frequently utilized in these types of campaigns. It’s believed that Dero offers higher payouts and has the same or better anonymizing capabilities, which may be the cause.
This involves setting up a “proxy-api”-named Kubernetes DaemonSet, which is then used to inject a malicious pod onto each node of the Kubernetes cluster to start the mining process.
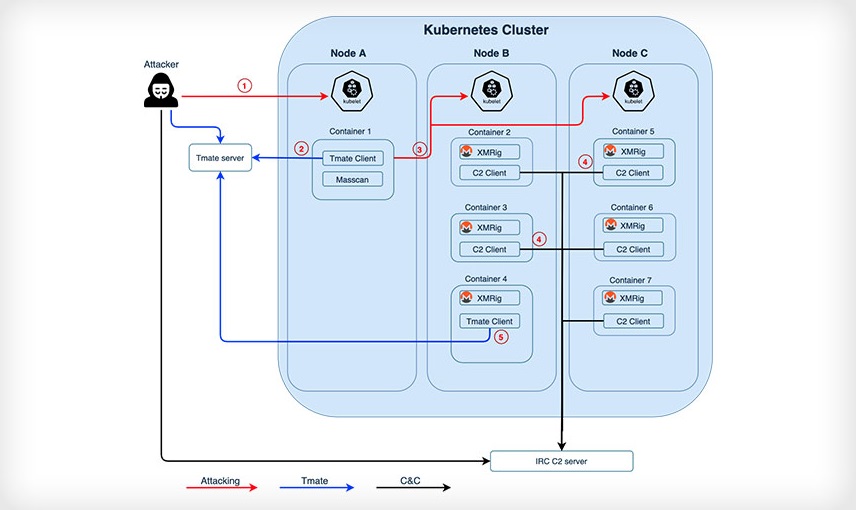
The attacks, which have been linked to an unidentified actor with financial motivation, start with a search for Kubernetes clusters that have authentication set to –anonymous-auth=true, allowing anonymous requests to the server. Additionally, attackers can drop initial payloads from three different U.S.-based IP addresses.
See more: Government and CIS energy targeted by YoroTrooper cyberspies
In order to do this, a Docker image containing a “pause” binary—which is really the Dero coin miner—is coordinated to execute by the DaemonSet’s YAML file.
In a legitimate Kubernetes deployment, “pause” containers are used by Kubernetes to bootstrap a pod in a legal Kubernetes deployment. “In order to blend in, attackers may have used the moniker to hide from detection.
The cybersecurity firm said that by attempting to remove the existing “proxy-api” DaemonSet linked to the Dero effort, it was able to identify a parallel Monero-mining campaign that was also aimed at vulnerable Kubernetes clusters.
See more: Hackers steal riot game source codes and demand a ransom
This is a sign of the continuous conflict between cryptojacking organization’s fighting for access to cloud resources in order to seize and maintain control of the computers and use all of their resources.
According to Benjamin Grap and Manoj Ahuje, threat researchers at CrowdStrike, both initiatives are competing to locate unknown Kubernetes attack surfaces.
Author: Komal Gaware
We hope you found article interesting. For more exclusive content follow us on Facebook, Twitter and LinkedIn