What is Petya ransomware – Latest Hacking Updates
Petya ransomware is a type of malware that caused significant damage to organizations around the world in 2017. Like WannaCry, Petya is classified as a worm because of its ability to spread rapidly across networks.
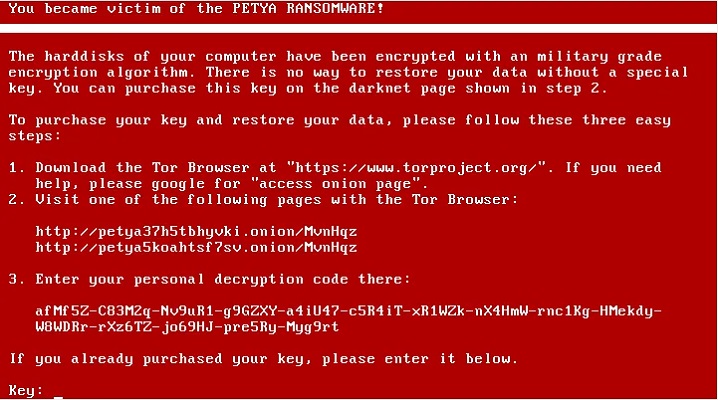
Petya works by encrypting the master boot record of a victim’s computer, which makes the entire system unusable. The malware then displays a message demanding payment in Bitcoin in exchange for the decryption key.
One of the notable features of Petya is its use of a technique called “wormable” propagation, which means it can spread rapidly through vulnerable networks, even if the initial infection is removed. Petya was able to exploit a vulnerability in the Windows operating system known as EternalBlue, which was discovered by the United States National Security Agency (NSA) and later stolen by hackers.
The Petya ransomware attack affected companies around the world, including shipping giant Maersk, pharmaceutical company Merck, and FedEx subsidiary TNT Express. The attack caused significant disruption to operations, as many companies were unable to access their critical data and systems.
In response to the attack, Microsoft released a security patch(CVE-2017-0143, CVE-2017-0144, CVE-2017-0145, CVE-2017-0146, CVE-2017-0148) for the EternalBlue vulnerability, and urged users to update their systems. However, by the time the patch was released, the damage had already been done.
To protect against ransomware such as Petya, organizations should take steps such as regularly backing up data, updating software and operating systems, and educating users on safe browsing habits. It’s also important to have an incident response plan in place, which can help mitigate the impact of an attack and reduce the risk of paying the ransom.
In conclusion, Petya ransomware was a significant cybersecurity event that highlighted the dangers of ransomware and the need for better protection measures. While the attack caused significant disruption and damage, it also led to greater awareness and action in the cybersecurity community to prevent similar attacks in the future. Organizations must take proactive measures to protect themselves against ransomware, including implementing regular backups, patching vulnerabilities, and educating users on safe browsing habits.
We hope you found article interesting. For more exclusive content follow us on Facebook, Twitter and LinkedIn






