YouTube tutorials produced by AI spreading info-stealing malware
Threat actors have been seen more frequently spreading stealth malware like Raccoon, RedLine, and Vidar via AI-generated YouTube videos.
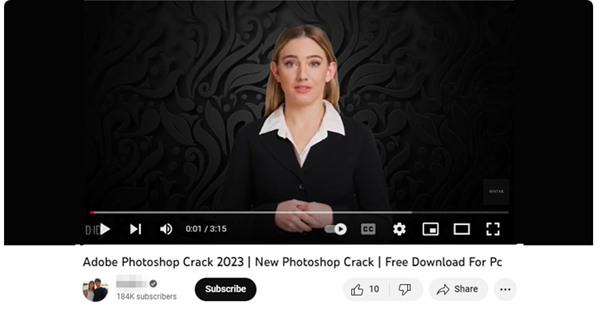
According to Cyber Firm researcher Pavan Karthick M, “The films entice visitors by claiming to be lessons on how to get pirated versions of software like Photoshop, Premiere Pro, Autodesk 3ds Max, AutoCAD, and other applications that are licensed products available only to paid users”.
The information thief ecosystem also consists of threat actors known as traffers who are hired to spread the malware using various techniques, just as the ransomware landscape consists of core developers and affiliates who are in charge of locating potential targets and actually carrying out the attacks.
YouTube is one of the most widely used platforms for the propagation of malware, and according to Security Firm, the number of videos with links to stealer malware in the description section has increased by 200–300% month over month.
In addition to being hosted on MediaFire, Google Drive, Discord, GitHub, and Telegram’s Telegra.ph, these URLs are frequently obscured using URL shorteners like Bitly and Cuttly.
Threat actors frequently target prominent accounts to quickly reach a big audience by using data dumps and social engineering to hijack legitimate YouTube accounts and spread malware.
See more: kamikakabot-malware-being-used-in-latest-dark-pink-apt-attacks
Karthick stated, “Uploading to such accounts offers video legitimacy as well. “Such YouTubers will, however, denounce the account thief to YouTube and reclaim control of their accounts within a day or two. Yet, hundreds of people may have been victims in a matter of hours.”
More concerningly, five to ten crack download videos are published to the video platform every hour, and the threat actors use SEO poisoning techniques to push the films to the top of the list.
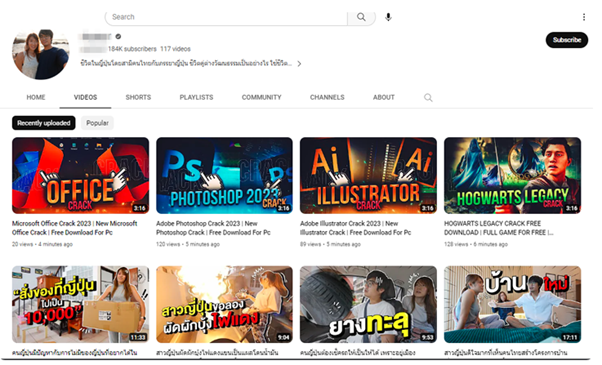
Threat actors have also been seen to post phoney comments on uploaded videos in an effort to deceive viewers and persuade them to download cracked software.
See more: batloader-delivers-vidar-stealer-and-ursnif-using-google-ads
The change coincides with an increase in new information-stealing variations including SYS01stealer, S1deload, Stealc, Titan, ImBetter, WhiteSnake, and Lumma that are for sale and have the ability to steal private information while impersonating well-known programmes and services.
Additionally, the results come in the wake of the revelation of a ready-to-use toolset dubbed R3NIN Sniffer, which can be used by threat actors to steal credit card information from compromised online stores.
Users are advised to use multi-factor authentication, stop from clicking on suspicious links, and stay away from downloading or using unlicensed software in order to reduce the threats posed by stealer malware.
Author: Komal Gaware
We hope you found article interesting. For more exclusive content follow us on Facebook, Twitter and LinkedIn






